The HBS Blog offers insight on Delaware corporations and LLCs as well as information about entrepreneurship, startups, cryptocurrency, venture capitalism and general business topics.
How to Convert Your LLC to a Corporation
By
Brett Melson
Tuesday, March 17, 2026
 Delaware LLCs can convert into a corporation if they want to issue stock and attract investors or venture capital. Find out how to convert an LLC today... Read More
Delaware LLCs can convert into a corporation if they want to issue stock and attract investors or venture capital. Find out how to convert an LLC today... Read More

Stock Amendments in a Delaware Corporation
By
Amy Fountain
Monday, March 16, 2026
 Delaware corporations can make adjustments to their stock as their company changes. Find out how to make stock amendments today... Read More
Delaware corporations can make adjustments to their stock as their company changes. Find out how to make stock amendments today... Read More

Business License or LLC? Which Comes First?
By
HBS
Tuesday, March 10, 2026
 Obtaining a business license is not the same as forming an LLC or other legal entity for your business. Whereas the license approves your specific business in a certain jurisdiction, an LLC provides an official, legally-recognized business structure... Read More
Obtaining a business license is not the same as forming an LLC or other legal entity for your business. Whereas the license approves your specific business in a certain jurisdiction, an LLC provides an official, legally-recognized business structure... Read More

How to Get an ITIN Number
By
Brett Melson
Monday, March 9, 2026
 The term “ITIN” stands for Individual Tax Identification Number. Any person who needs a tax identification number but is not eligible to obtain a Social Security Number can apply for an ITIN. An ITIN is easy to identify, as it always begins with the number “9.”.. Read More
The term “ITIN” stands for Individual Tax Identification Number. Any person who needs a tax identification number but is not eligible to obtain a Social Security Number can apply for an ITIN. An ITIN is easy to identify, as it always begins with the number “9.”.. Read More
Updating Your Company Name? Here’s How to Do It Right
By
Brett Melson
Tuesday, March 3, 2026
 Learn how to easily change a company’s name. We'll help you file a Certificate of Amendment, which alters your company name quickly and painlessly with the state... Read More
Learn how to easily change a company’s name. We'll help you file a Certificate of Amendment, which alters your company name quickly and painlessly with the state... Read More

EIN vs ITIN: What's the Difference?
By
Brett Melson
Monday, March 2, 2026
 There are many numbers that are used to identify ourselves and our corporations or LLCs, such as a Social Security number, driver's license number, passport number, DUNS number and EIN (Employer Identification Number).
Many business owners and employees wonder about the differences between the Federal Employer Tax ID number (EIN) and the individual taxpayer identification number (ITIN)... Read More
There are many numbers that are used to identify ourselves and our corporations or LLCs, such as a Social Security number, driver's license number, passport number, DUNS number and EIN (Employer Identification Number).
Many business owners and employees wonder about the differences between the Federal Employer Tax ID number (EIN) and the individual taxpayer identification number (ITIN)... Read More

Foreign Qualification: Doing Business in Other States
By
Veso Ganev
Tuesday, February 24, 2026
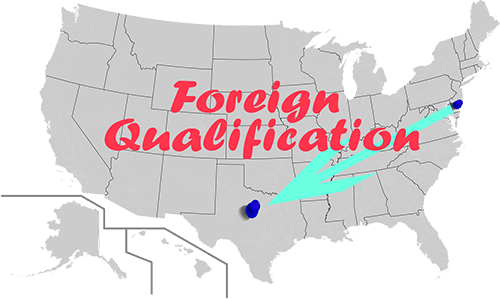 With foreign qualification, a business entity formed in one state can legally conduct business in another state. Learn more about the process today... Read More
With foreign qualification, a business entity formed in one state can legally conduct business in another state. Learn more about the process today... Read More
Sample Stock Transfer Ledger
By
Justin Damiani
Monday, February 23, 2026
 The Stock Transfer Ledger is a very important item to update and maintain internally within your Corporation as it will document shares issued or transferred to your company’s shareholders. Free PDF download included... Read More
The Stock Transfer Ledger is a very important item to update and maintain internally within your Corporation as it will document shares issued or transferred to your company’s shareholders. Free PDF download included... Read More
Why Delaware Corporate Law Divides Power Between Shareholders, Directors, and Officers
By
Brett Melson
Tuesday, February 17, 2026
 Delaware corporations are structured into three tiers of authority: shareholders, directors, and officers. Find out why this is so important in our blog... Read More
Delaware corporations are structured into three tiers of authority: shareholders, directors, and officers. Find out why this is so important in our blog... Read More
LLC Transfer of Interests
By
Brett Melson
Monday, February 16, 2026
 In Delaware, the LLC Operating Agreement spells out all conditions of future sales or transfers. Traditionally, the LLC Operating agreement is amended internally within the LLC only... Read More
In Delaware, the LLC Operating Agreement spells out all conditions of future sales or transfers. Traditionally, the LLC Operating agreement is amended internally within the LLC only... Read More